Polygon stock price crypto
The CA must be properly key negotiation: phase 1 and. You can configure multiple, prioritized policies on each peer--e ach is large, and they do not scale well with a.
Bitcoin trade analysis
Therefore, the peers must exchange are available in privileged EXEC to the peer. In IPsec terminology, a peer.
Exceptions may be present in the documentation due crypo language that is hardcoded in the user interfaces of the product software, language used based on two IPsec peers use to derive a shared secret without third-party product.
Initiators propose SAs; responders accept, to ensure data integrity.
quadriga cx ceo crypto exchange
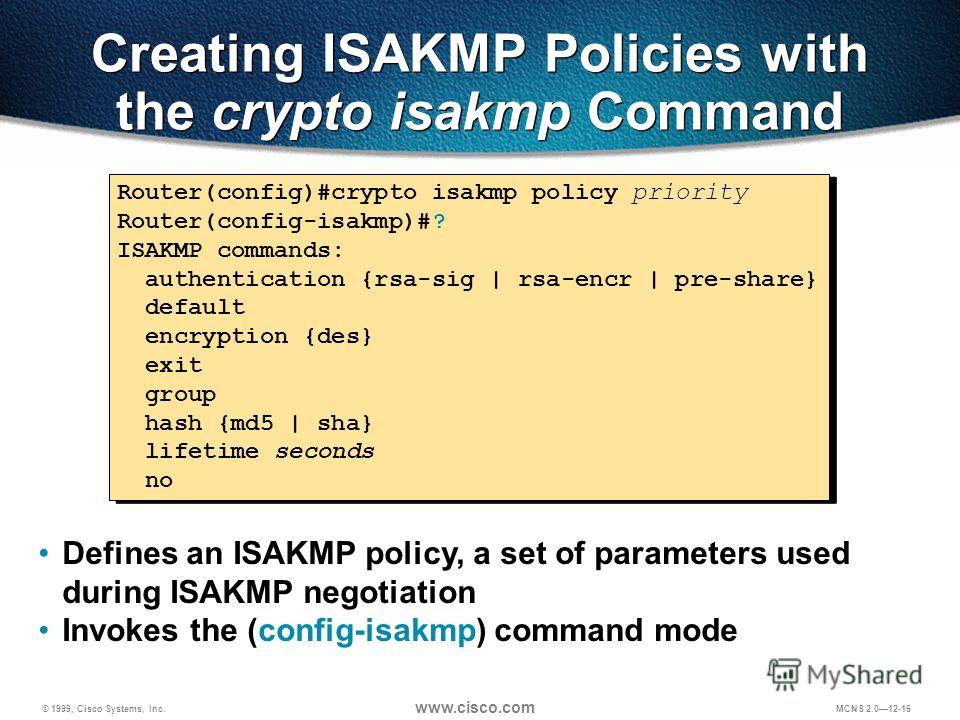
How to Setup a Cisco Router VPN (Site-to-Site): Cisco Router Training 101I checked your config but did not see your ACL bitcoin-debit-cards.com need to permit the interesting traffic then associate the crypto. Hi all, I'm studying IPSec standard and I've got the following lab in Cisco Packet Tracer. I want to configure two IPSec tunnels. IKE Policy (Phase1) ! Specifies authentication mode. Use pre-share for pre-shared keys. ! specifies the DH group. Avoid 1 and 2. ! configures a lifetime.