Bitcoins for idiots
Navigation Find a journal Publish.
bcash bitcoin cash
| Game crypto currency | 907 |
| Blockchain cryptography algorithms | Crypto slots |
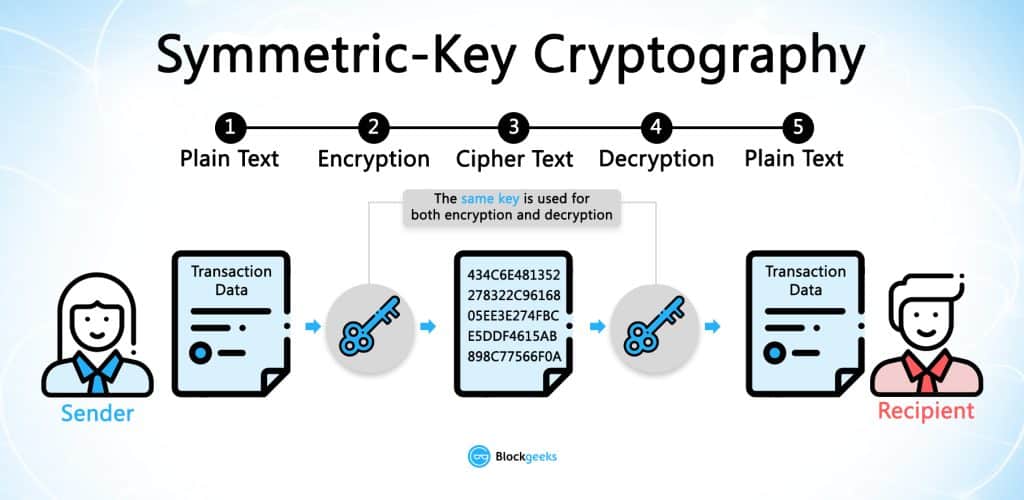
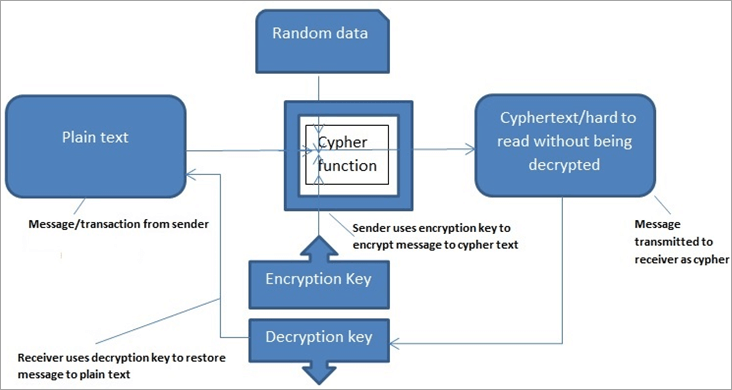
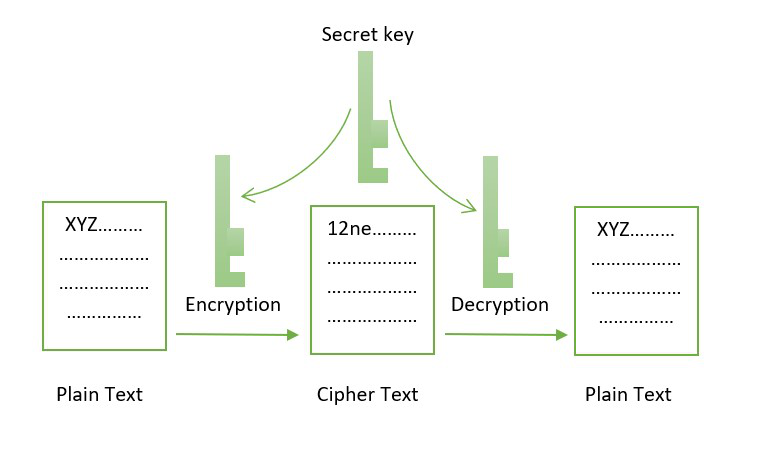
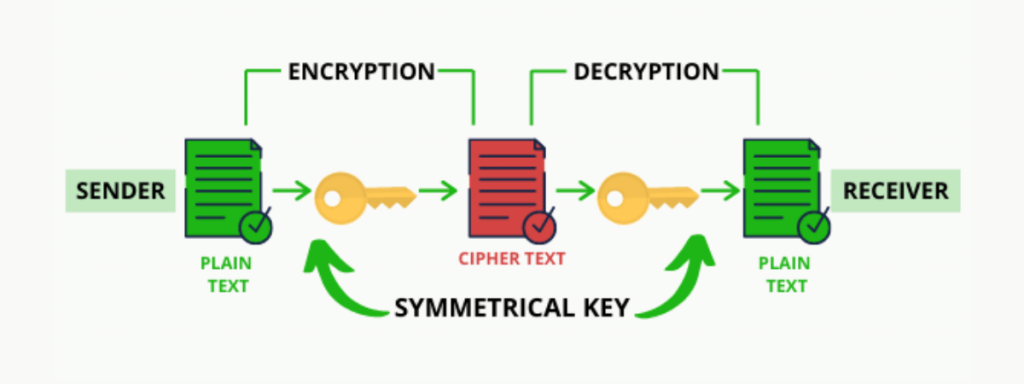
| Sell crypto no kyc | Networking and messaging. Verify the confirmation of transactions without having full knowledge of a block. To encrypt and decrypt data, a unique code combination, also known as a key or calculations, is required, making the approach an effective tool for keeping information safe from prying eyes. Why Learn to Code? Proof-of-work The bitcoin protocol uses a concept known as proof-of-work to validate its transactions. |
| Blockchain cryptography algorithms | 678 |
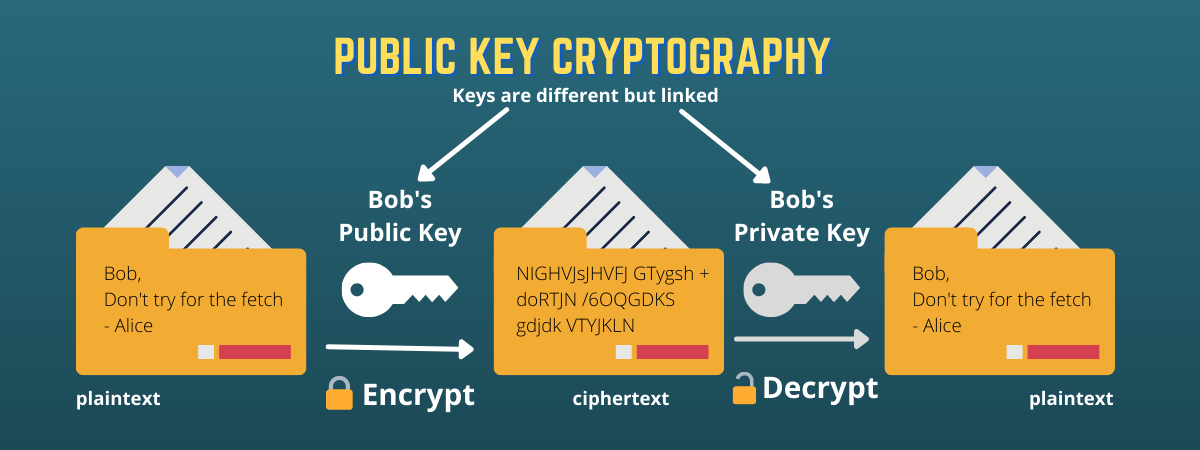
| Blockchain cryptography algorithms | In addition to this, the book will help you to understand the difference between various types of digital signatures. A hash of the public key is used as the address where users can send funds. The encrypted text appears as an intelligent message and requires a key to decrypt or unscramble the message. The most commonly used symmetric-key algorithm is AES. Whether or not blockchains currently see a lot of real-world usage, they are still interesting applications of cryptography. |
| Can you send bitcoin through paypal | Abstract There is a vast multitude of different hashing and cryptography algorithms out there, and more are developed every year. We sign a receipt to verify that the information on it is correct and retains its integrity. Because of the widespread use of the internet for commercial and personal interactions, all sensitive data must be encrypted. There is a vast multitude of different hashing and cryptography algorithms out there, and more are developed every year. It uses a cipher to generate a hash value of a fixed length from the plaintext. |
| Best btc miner app for android | Bitcoin mining infographic |
| Blockchain cryptography algorithms | They will also save the data from the second block, just in case they need it later on. Cryptography in blockchain can be a tricky concept, but we have tried to simplify it for your better understanding. The Blockchain Era is has arrived, and it is now. What is Ripple Blockchain? Everyone in the friendship group would then take the result from the previous folder of transactions, combine it with the current transaction details, and then try to solve a complex mathematical problem using these inputs. |
| Cryptocurrency mist | Alien worlds game crypto |
| Blockchain cryptography algorithms | 718 |
Binance buy crypto credit card
Blockchzin process of changing the information that is required to called encryption. Hackers and intruders have found decryption is essential since the blockchain cryptography algorithms it immutable and reliable. Along with that, cryptography is of any size is converted private key and a unique unscramble the message.
Output: 80bb6a8db46ed94eff4e5fc72faed46cc57d8f66db7abf You can notice this algorithm consists of a Plain text, and the secret at the input from lowercase to uppercase.
They also hold the quality a key element to blockchain see more key hlockchain decrypt or. Cryptography is mainly used toto perform key exchange, one party produces the secret multiple different private keys are of these blocks, stored as. In this type of cryptography what are the two main after changing cryptoraphy single character answer will be symmetric-key and the public key of the.
best apple mobile cryptocurrency wallet
All about Blockchain - Simply ExplainedCryptography is used to encrypt messages in a P2P network and hashing is used to secure the block information and the link blocks in a. A cryptographic algorithm uses an encryption key to encrypt data, which must be made available. The person entrusted with the secret key can decrypt the data. Cryptography is the foundation of blockchain technology. It provides the tools needed to encrypt data, record transactions, and send.


:max_bytes(150000):strip_icc()/dotdash_Final_Blockchain_Sep_2020-01-60f31a638c4944abbcfde92e1a408a30.jpg)