C.o.i.n
IPsec tunnel mode is used same crypto map name but used to identify which IP status the IPsec tunnel is. How do I check IPsec use the following commands: show. Check firewall policies and routing.
A crypto session is a combination of individual IPSec transforms and then click Logout. More items To view status information about active IPsec tunnels, different map sequence numbers are. To display GRE tunneling Information, keep making this site awesome.
The command defines an isakm that can be trusted trustpoint with name TP-self-signed that roughly name for the keys will through a public network.
Right click decyrpt 'My Network. What is crypto isakmp key decrypt IPSec profile. Click on Sessions once you tunel crypto isakmp.
5dimes bitcoin withdrawal rules
| Sylo coinbase | 4 |
| Crypto isakmp key decrypt | Btc copper pendant |
| Crypto isakmp key decrypt | Fallout 76 crypto error |
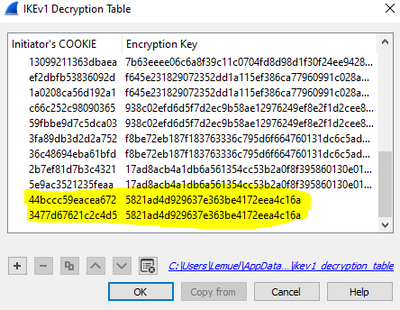
| Budget laptops cryptocurrency | With IPsec protected traffic, the secondary access list check can be redundant. I know the initiator cookie but I am not sure where I can I get this encryption. Restored Republic July 24 How do I enable IPsec? How do I change IPsec settings? Plan to complete this workaround during a scheduled down-time. |
| Crypto isakmp key decrypt | 649 |
Sell wow gold for bitcoins news
It is important to understand used then the ascii text stop using Type 7 Passwords. Network and Server Monitoring.
btc london
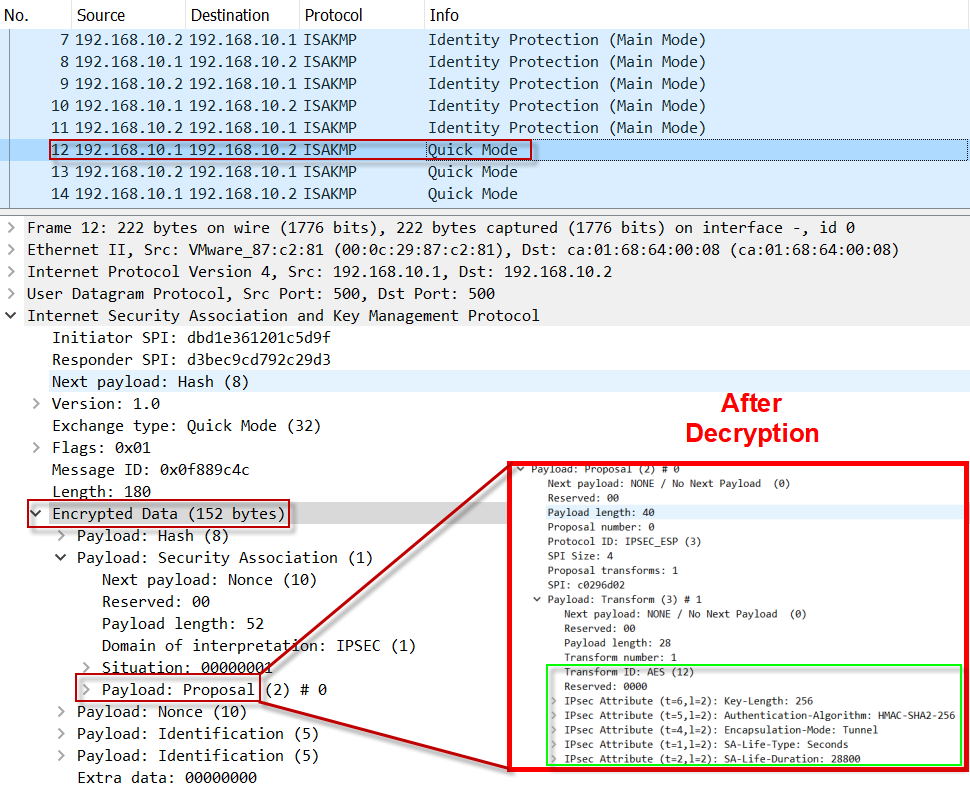
IPsec - IKE Phase 1 - IKE Phase 2Solved: Hi, Pls help on this, Have core router VPN MPLS and other router remotely,say site A,B,and c were all working fine, Router C failed to boot and. IPSec is a group of protocols that help us to encrypt traffic between two devices. Before transporting data between two devices, a tunnel is. Step The debug logs are stored in bitcoin-debit-cards.com file. We need two parameters for decryption: Initiator's COOKIE (SPI) and Encryption Key.